Last week, a local privilege escalation vulnerability was introduced in the Polkit component, affecting every major Linux distribution. Polkit is a component for controlling system-wide privileges in Unix-like operating systems. It allows a non-privileged process to communicate with privileged ones.
This memory corruption vulnerability, which got the name PwnKit, exploits a bug in polkit’s pkexec utility where it doesn’t handle the calling parameters count correctly and ends trying to execute environment variables as commands.
This easily exploited vulnerability, which received a CVSS score of 7.8, allows any unprivileged user to gain full root privileges on a vulnerable host by exploiting this vulnerability in its default configuration. The exploit to this vulnerability was published and is now available to all.
To mitigate this vulnerability, it is necessary to update the operating system and patch this vulnerability. If full patching is not an option at the moment, an example of a temporary workaround would be to remove the SUID-bit from pkexec:
# chmod 0755 /usr/bin/pkexec
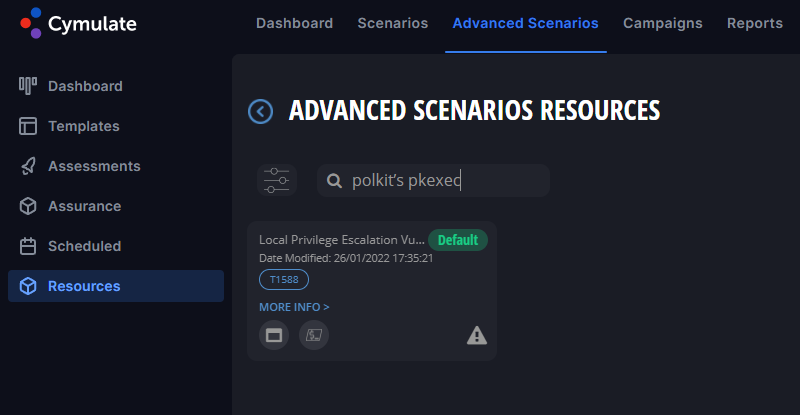
Cymulate’s Research Team released a PoC of the exploit part of the Advanced Scenarios module at the Cymulate platform. Whilst exploiting the vulnerability, it does not cause any harm to the endpoint or the corporate network.