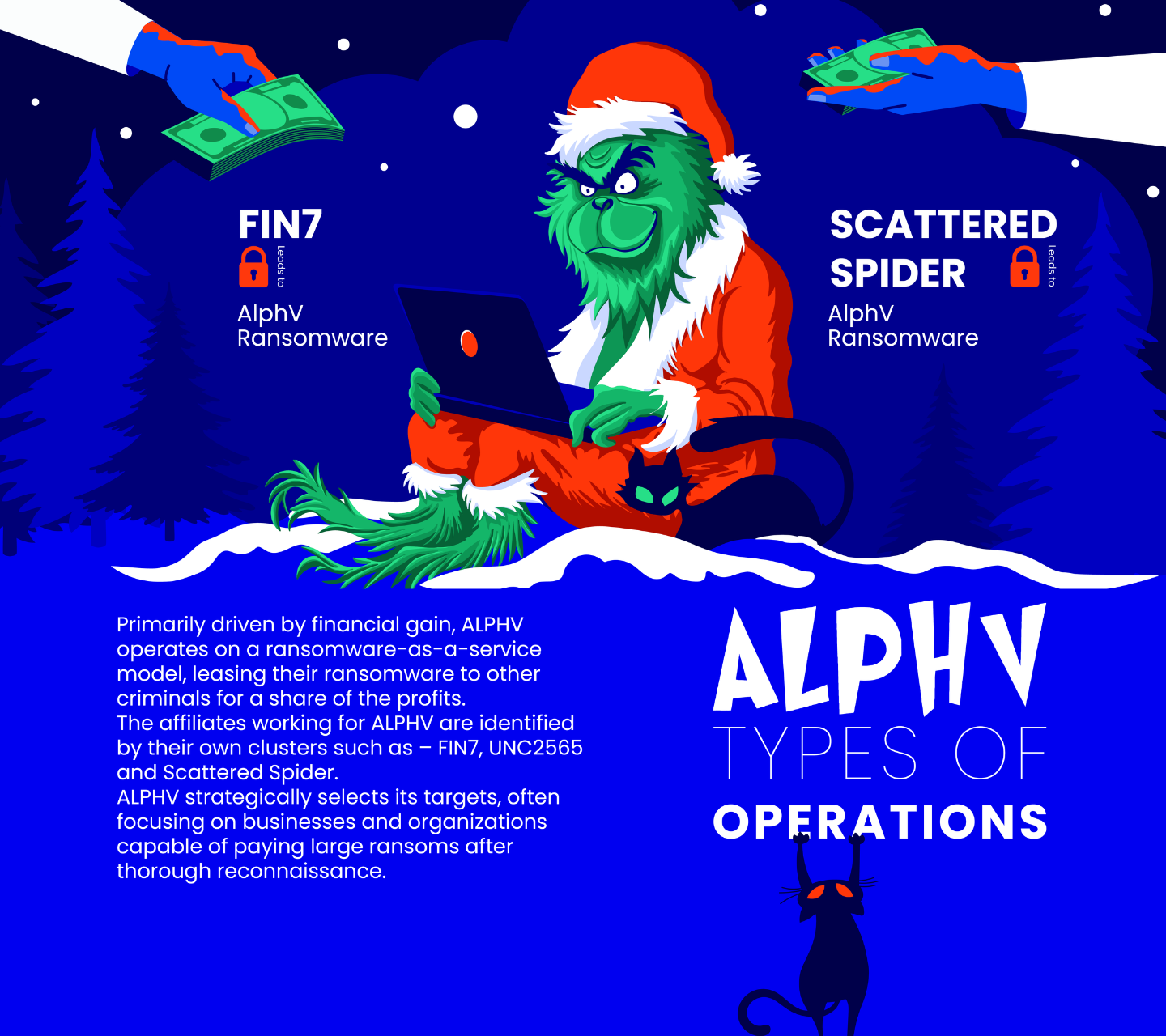
In the digital landscape, a Grinch-like figure exists, not seeking to steal Christmas, but something potentially more valuable: your data. ALPHV Ransomware, also dubbed BlackCat, prowls in the cyber shadows, ready to pounce on any network vulnerability it finds.

ALPHV Ransomware: The Stealthy Cyber Grinch
This sophisticated cyber threat operates quietly, with a potency that can leave businesses and governments bereft of their operational data. Its tactics are varied, but the goal is singular: to hold your data hostage and demand ransom.
What Are ALPHV Ransomware’s Favorite Attack Techniques
ALPHV doesn't slide down chimneys but through security gaps and unsuspecting clicks. Its preferred methods include:
- Phishing campaigns: Crafting deceptive emails to trick users into granting access.
- Exploiting vulnerabilities: Targeting unpatched software to sneak into systems.
- Credential theft: Swiping login details to move laterally within a network.
- Double extortion: Not just encrypting data but threatening to leak it unless the ransom is paid.
Proactive Steps Against ALPHV's Grinchy Grip
To protect your digital domain from this silent Grinch, follow these proactive steps:
- Empower your team with knowledge to recognize and avoid phishing attempts.
- Maintain a regiment of regular updates and patches to close off known vulnerabilities.
- Implement stringent monitoring to spot and stop suspicious activities promptly.
- Install robust anti-malware defenses that are adept at detecting and thwarting ransomware attacks.
- Divide and conquer with network segmentation, making it harder for any breach to spread.
- Back up your data religiously, ensuring you have a fallback plan that doesn't involve paying ransoms.
Streamlining Defense with Cymulate's Simulations
-
Immediate Threat Simulations: Quickly identify and reinforce weak points against ALPHV tactics like phishing and vulnerability exploitation.
-
Advanced Scenarios: Tackle sophisticated APT patterns with scenarios such as FIN7, enhancing preparedness for complex attacks.
Using Cymulate's simulations ensures your cybersecurity is proactive, agile, and ready for the challenges posed by evolving ransomware threats.

Stay informed, stay prepared, and keep ALPHV Ransomware out of your network's equation.



