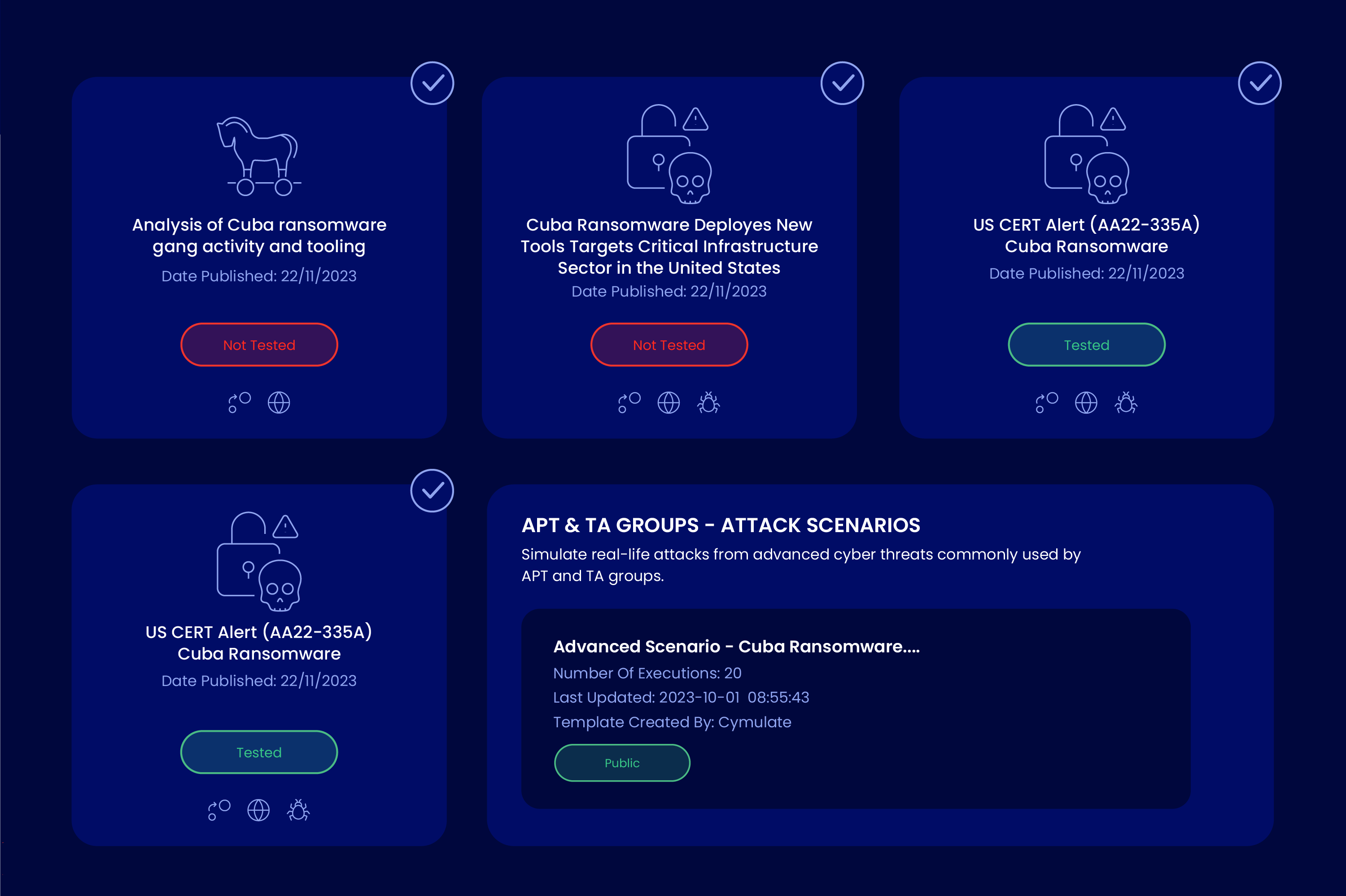
In line with our monthly threat dissection, today, we dig deep into the Cuba Ransomware threat.
What is Cuba Ransomware
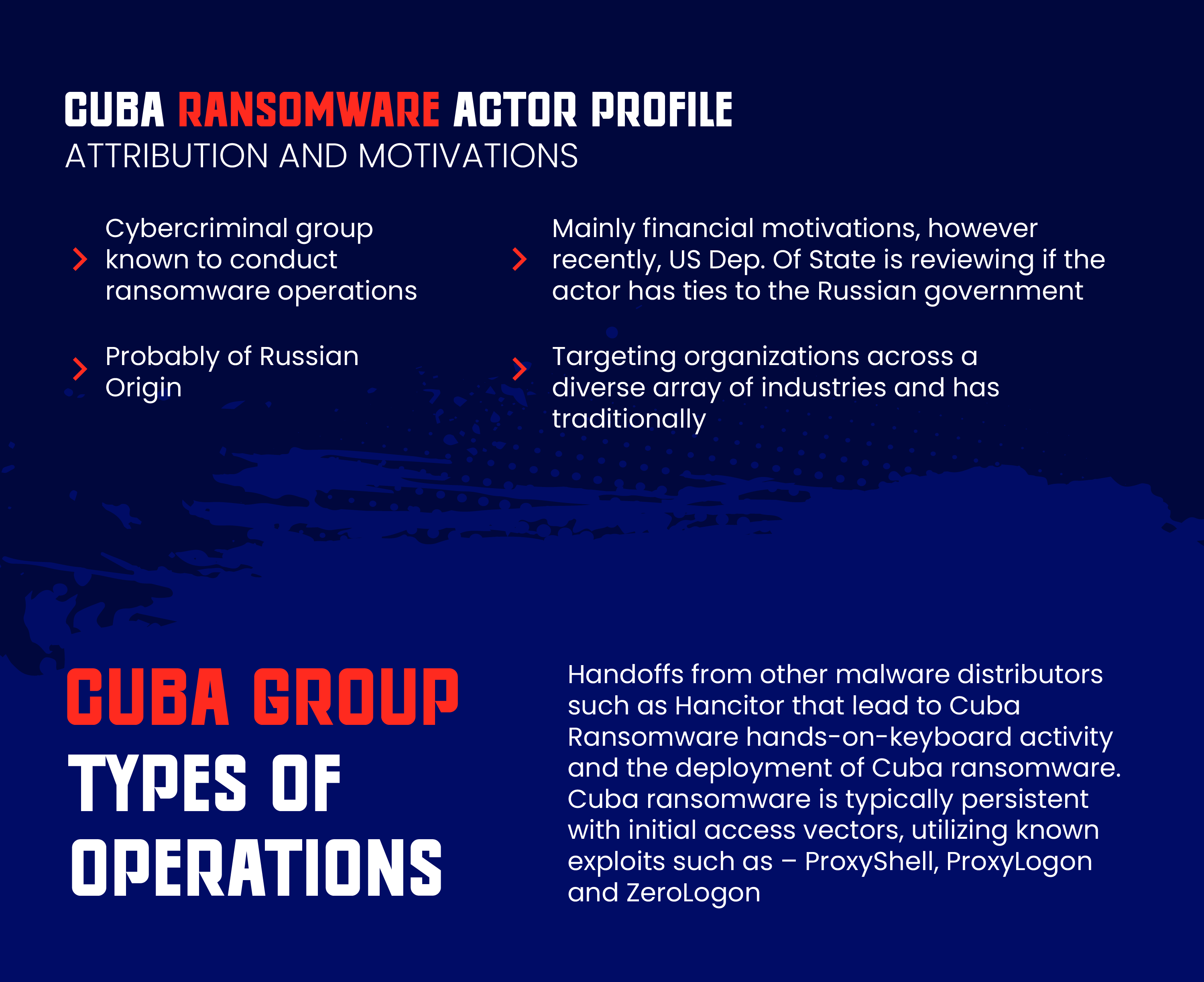
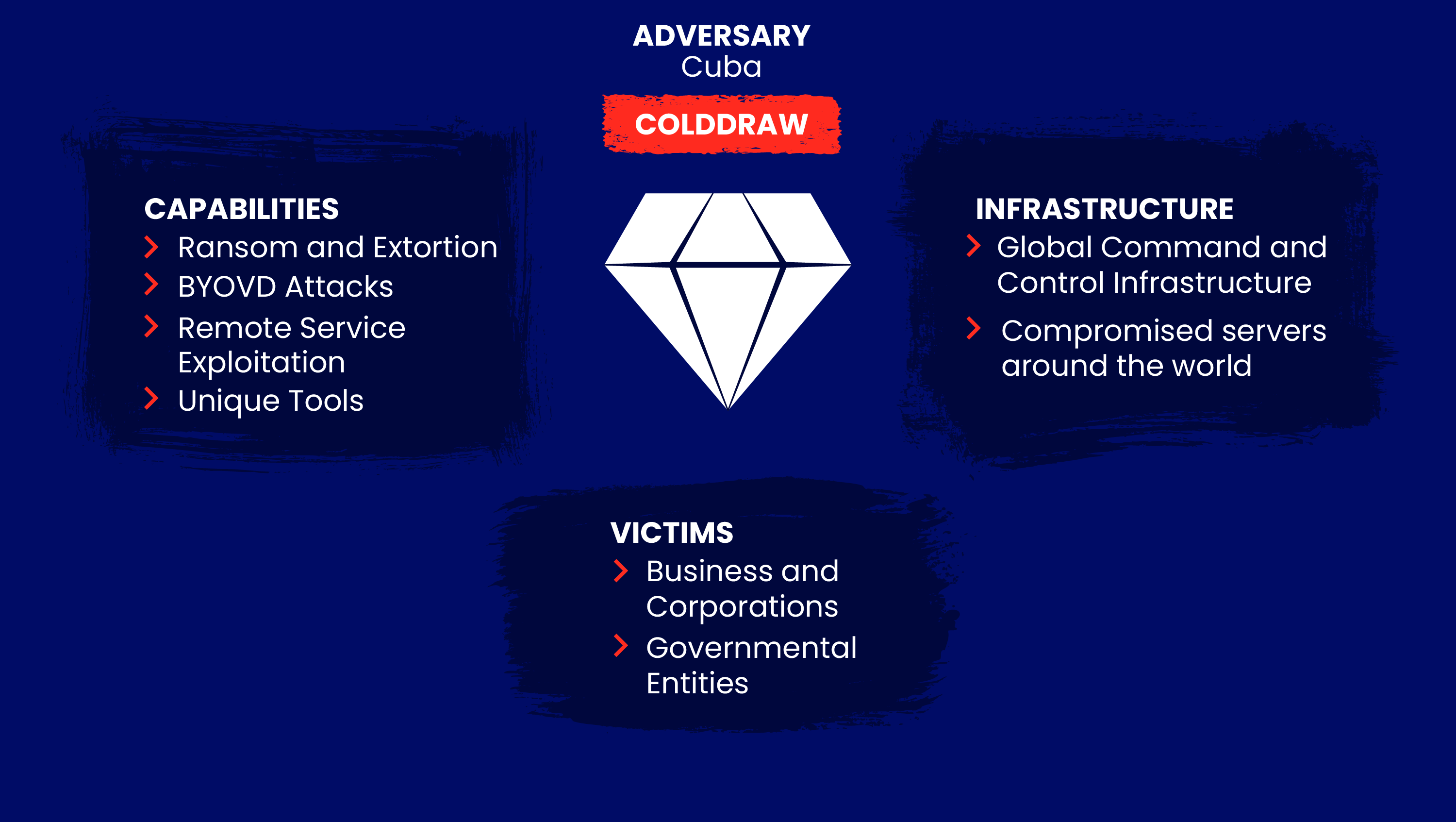
The Cuba Ransomware group is a dangerous cyber threat globally. Despite its name, it reputedly originates from Russia and has accumulated over $13 million worth of Bitcoin from victims. Cuba Ransomware utilizes sophisticated techniques to penetrate networks, disable security controls, and encrypt data.
What Are Cuba Ransomware’s Favorite Attack Techniques
To gain initial access, Cuba Ransomware often exploits common vulnerabilities such as unpatched Microsoft Exchange servers using ProxyShell or ProxyLogon. They also look for vulnerabilities in VMWare's VCenter backup system. Once inside the network, the hackers use malicious loaders like "Bug Hatch" to deploy next-stage payloads.
A particularly nasty technique used by Cuba Ransomware is known as "bring your own vulnerable driver" (BYOVD). They use vulnerable but signed kernel drivers from legitimate software, like antivirus programs, to disable security services from the kernel level. Even if the driver's certificate is revoked, it can still be loaded in Windows.

How to Preempt Attack Success
To defend against Cuba Ransomware, you can:
-
Patch, upgrade, and update internet-facing servers, workstations, and critical software. This removes vulnerable entry points like outdated Exchange servers.
-
Implement robust vulnerability management to identify and prioritize vulnerabilities across the environment.
-
Monitor for unusual events like new user creation, RDP being enabled, and unexpected kernel driver installation.
-
Use behavior-based anti-malware on critical servers like Exchange to detect advanced techniques.
-
Segment networks to limit lateral movement after a breach.
-
Back up data regularly and keep backups offline and immutable to allow recovery without paying ransom.
Cuba is reputed for its cigars and beaches, but better stay clear of its ransomware 😉
Stay safe!