What is the rationale behind Cymulate's recommendation to block specific file types (highlighted in red...) in the Web Gateway Report(Inbound)?
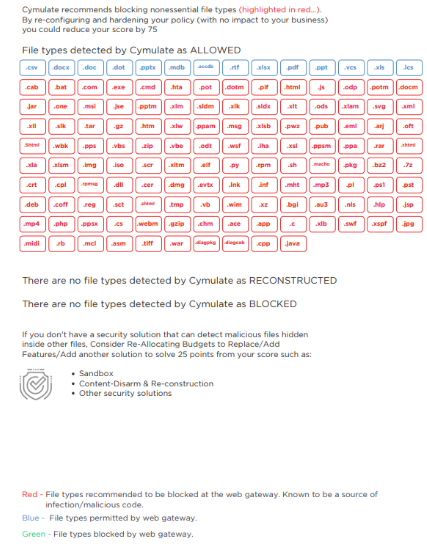
Our customer is curious about the rationale behind blocking these file types.
(It would be even better if there is official documentation or information explaining the basis for this.)
Best regards.